"PETYA" RANSOMWARE - A GLOBAL OUTBREAK
On Tuesday, June 27, 2017, a Petya ransomware variant (also called Petrwrap or and NotPetya) began spreading across Europe and the U.S., making its way as far as Australia.
Victims so far include Ukrainian power companies, airports, public transit, and the central bank, Danish shipping company Maersk, the Russian oil giant Rosneft, Merck pharmaceuticals in the U.S. and numerous institutions in India, Spain, France, the United Kingdom, and beyond. In short - everyone is on the attackers’ radar.
Like the recent WannaCry attacks, “Petya” uses the NSA exploit EternalBlue, as well as an alternate exploit, to rapidly propagate through networks. The ransomware demands $300 in Bitcoin to decrypt but its real intent appears to be wholesale destruction. Some samples of the attack delivers an additional payload, an information stealer and hacking tool that allows it to infect other machines via Windows Sysinternals, even if they are not vulnerable to EternalBlue.
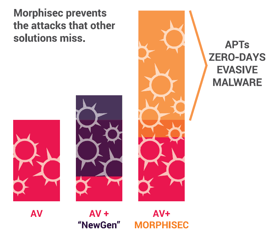
“Petya” is yet another example of an ever-evolving threat landscape. These sophisticated, advanced attacks become more common by the day, accounting for up to 40% of today's cyber attacks. To secure your company, you need to proactively deal with these new attack techniques. Unlike “Petya” , fileless, in-memory attacks leave no trace and may be siphoning data without you even knowing.