March 15th, 2023
Windows Protector
- Ransomware anti-encryption service was added. The Anti-Ransomware service prevents the encryption phase by killing the process preforming the encryption, stopping the attack and keeping your data safe.
Note: The ransomware service deploys decoy files in the file system.
- UAC Bypass protection was enhanced, adding the prevention of injection to high-privilege processes in addition to our prevention of process spoofing.
- We added the ability to control DLL splitting.
- Reflective PE/DLL Loading protection was added as a beta feature (notifications only).
- RDP Credential Theft protection was added as a beta feature (notifications only).
- Additional protection was added to DCSync Credential Theft protection as a beta feature (notifications only).
- Chrome credential theft protection was improved to reduce false positives.
- SAM Hashes protection was moved from beta to production.
- The Protector was hardened to prevent tampering. Additionally, we blocked the ability to stop more Morphisec processes.
December 11th,2022
- On the applications list in Vulnerabilities, you can now filter and search by machine name.
This means that you can easily find all vulnerabilities, by machine and patch.
Click More Options in the top right and then Machines are searchable on the left-hand side.
November 8th, 2022
Cloud
- SAM Hashes protection was moved from beta to production. You can set it to Alerts or Prevent. Protector version 5.13 is required to enable this feature.
- Script Execution was moved from beta to production. You can set it to Alerts or Prevent. Protector version 5.13 is required to enable this feature.
- Protection from Local LSASS Dump was added to the Credential Theft feature.
October 3rd, 2022
Cloud
- In Central Update, you can now use a substring to search for protectors.
Cloud
- Threat Categories have been changed to Classification and Sub-Classification to provide more granularity.
- Applications were added to the default protection plans. New applications are added automatically to the default plan for new installations. For existing installations, you need to add them manually.
August 1, 2022
Cloud
Cloud
- The Threat table can now be exported as CSV file in addition to exporting threat logs as JSON.
- The error when updating multiple protectors using Central Update was fixed.
- The inability to cancel updates in Central Update was fixed.
- sdiagnhost.exe was added to the default protection plans.
JULY 7, 2022
Cloud
- We improved the detection mechanism to reduce the number of false positives for Shadow Copy mitigation from Veeam backup.
- We improved the detection mechanism to reduce the number of false positives for credential theft from Google Chrome.
JUNE 28,2022
Cloud
Cloud
Admin or Root users can now reset the login credentials (password and MFA) for specific users. The user’s next login is then treated as a first login. The user receives an email to log in with a new password and reset their MFA.
June 18th, 2022
Cloud
- Scout now includes the capability to filter Applications for clients, servers, or VDIs.
- Scout has more entry points from the Scout Overview. Patches available, and the Top 5 widgets in the Affected Applications tab now link to filtered lists.
- Executables that erroneously appeared in the applications list in Scout were removed. Now only installed applications appear.
MAY 12, 2022
Cloud
MFA (multi-factor authentication) with Google Authenticator is now available as an additional security layer for the Morphisec Security Center. When enabled, users login with their username, password, and a one-time authentication code generated by the free Google Authenticator app to access the Morphisec Security Center.
May 11, 2022
Cloud
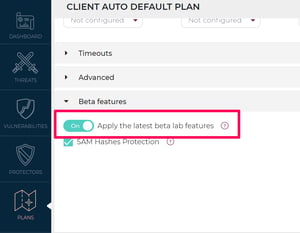
New advanced protection mechanisms join the Morphisec beta program.
Beta features are turned on in alert-only (not protecting) mode, and a successful beta run allows us to deliver our most cutting-edge protection features faster, further reducing your organizational risk and attack surface.
This release includes:
This release includes:
-
AMSI Bypass protection - Sends alerts for attempts to bypass the Windows Antimalware Scan Interface (AMSI).
The Microsoft Antimalware Scan Interface (AMSI) provides a way for software to talk to security products, requesting scans of files, memory, or streams for malicious payloads, regardless of vendor. The Antimalware Scan Interface works with Microsoft Defender to scan relevant data for malicious payloads, and as such, plays a critical role in keeping Windows 10 and Windows Server systems from being compromised.
The Antimalware Scan Interface is used by most EDR solutions to scan for suspicious payloads, and if this solution has been tampered with, EDR solutions will lose their visibility into this critical functionality. -
Chrome credential theft protection - Sends alerts upon attempted theft of passwords saved in Chrome. Once credentials are obtained, they can be used to perform lateral movement and access restricted information.
Note: credential theft prevention in Microsoft Internet Explorer and Edge are production features.
To configure your beta settings, go to Plans > Beta Features.
APRIL 26, 2022
Cloud
More SSO options are now available, so integrating with existing applications in your environment is easier than ever! In addition to Okta and Google Suite, you can now use Azure and OneLogin to access the Morphisec Security Center. For more information and to set up your SSO connection, please contact support@morphisec.com.
April 4, 2022
Cloud
Added support for WPD (Windows portable devices). Support for Microsoft's native device control feature in all elements of the Morphisec Security Center dashboards and widgets for enhanced visibility into your security posture.
March 15, 2022
On-Prem, Cloud
New Linux protector version 2.5 brings on-prem over-the-air updates. These maximize protection for newly released LTS kernels, and minimize unnecessary operational overhead and latency associated with the discovery, distribution, and application of new or improved protection. Learn more about Morphisec protector for Linux—contact suppport@morphisec.com.
February 15, 2022
Cloud, On-Prem
On-PremC:/Users and C:/Temp are now recommended in the default protection plans.
January 26, 2022
Cloud
New in production - PrintNightmare protection! PrintNightmare, a critical security vulnerability affecting the Microsoft Windows operating system (CVE-2021-34527 and CVE-2021-1675), is an authentication bypass exploit that leads to Local Privilege Escalation.
New in production - Shadow copy deletion prevention! Shadow copy deletion is a common early stage in a ransomware attack.
Defender detections, as well as Morphisec, prevented threats, can now be sent to the organizational SIEM.
January 15, 2022
Cloud
In Morphisec Scout, there is a new view in the Overview pane for "affected machines" which shows the risk breakdown by license type (client, server, VDI).

January 4, 2022
Cloud
Added KeePass, osqueryd, nginx, and httpd to default protection plans.
How to Give Feedback
We welcome your feedback about beta features at product@morphisec.com.
We welcome your feedback about beta features at product@morphisec.com.



.png?width=571&height=160&name=iso27001-(2).png)